The fastest, simplest distributed state enforcement engine ever built.
One server. One binary agent. Seven operating systems. 73 built-in resource types. Zero database queries on the check-in hot path. 10,000 nodes at 15-second check-ins on a single 4-core server.
Free for up to 25 nodes. No credit card. No time limit.
How Vigo compares
All figures based on a single server with 4 vCPU, 8 GB RAM, SSD. Vendor-documented requirements where available. Vigo figures are theoretical (benchmark-derived). Full methodology →
| Vigo | Puppet | Ansible | Chef | Salt | CFEngine | |
|---|---|---|---|---|---|---|
| Server processes | 1 | 3–5 | 1+ | 3+ | 2+ | 1–2 |
| Nodes @ 5 min | 50,000* | 100–500 | N/A (push) | 500–1,000 | 1K–5K | ~1,000** |
| Nodes @ 1 min | 25,000* | 50–100 | N/A (push) | 100–200 | 500–1K | ~500** |
| Nodes @ 30 sec | 15,000* | 25–50 | N/A (push) | 50–100 | 200–500 | ~250** |
| Nodes @ 15 sec | 10,000* | 10–25 | N/A (push) | 25–50 | 100–250 | ~125** |
| Check-in latency | ~300 µs | 100+ ms | N/A (push) | 50+ ms | ~1 ms | ~1 ms |
| DB queries per check-in | 0 | 5–10 | N/A | 3–5 | 0 | 1 (Enterprise) |
| Server RAM at 10K nodes | ~50 MB | 8–16 GB | N/A | 4–8 GB | 2–4 GB | 80 GB* |
| Agent binary | ~5 MB | ~200 MB | None | ~100 MB | ~50 MB | ~3 MB |
| Config language | YAML | Puppet DSL | YAML + Jinja2 | Ruby DSL | YAML + Jinja2 | Promise DSL |
| External database | None | PostgreSQL | None | PostgreSQL | None | PostgreSQL (Enterprise) |
| Bootstrap time | 30 seconds | 5–10 minutes | 0 (SSH) | 5–10 minutes | 2–5 minutes | ~1 minute |
| OS platforms | 7 | 3 | Any (SSH) | 3 | 3 | 4 |
* Vigo figures are theoretical — derived from internal benchmarks, not production deployments. Competitor estimates at sub-5-minute intervals are extrapolated from their architectures: Puppet and Chef perform server-side catalog compilation (1–3 seconds CPU per node per check-in); Salt uses lighter state compilation over ZeroMQ; CFEngine serves compiled policy but its Enterprise PostgreSQL reporting hub is the bottleneck (~8 MB/node). ** CFEngine Enterprise hub figure. Puppet PE requires 10–24 GB RAM for 100–2,500 nodes (PE 2025 docs). None of these tools officially support sub-5-minute check-in intervals. Full comparison with sources →
Capacity
10,000 nodes @ 15 sec
On a single 4-core server. 15,000 at 30-second intervals. 50,000 at 5-minute intervals. No compile masters, no worker pools, no database clusters. Performance analysis →
Speed
~300 µs per check-in
Cache-hit check-ins complete in microseconds, not milliseconds. No catalog compilation, no Ruby interpretation, no database round-trips. The server processes 3,300 check-ins per second on a single core.
Cost
25 nodes free. Forever.
No enterprise-only features. No gated add-ons. Every feature works at every tier. See pricing →
Simplicity
YAML. Not a DSL.
No custom language to learn. No compiler. No Ruby, no Python, no JVM on managed nodes. A sysadmin unfamiliar with Vigo can read a config file and understand what it does. One format, one directory, one publish command.
Features
73 built-in resource types
Files, packages, services, users, cron, Docker, IIS, registry, ACLs, firewall, certificates, network devices. 7 OS families. 33 trait collectors. 22 compliance frameworks. Browser-based SSH and RDP. See all features →
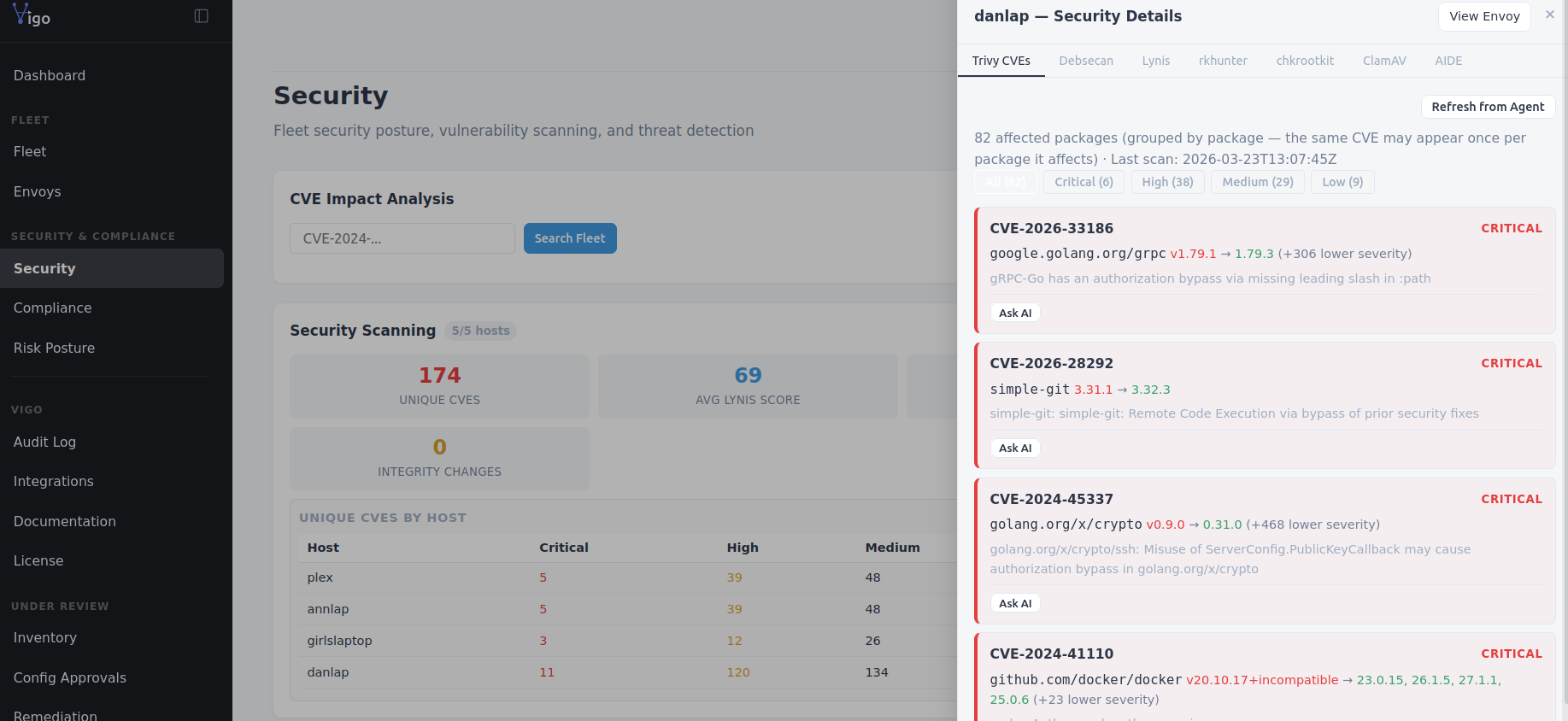
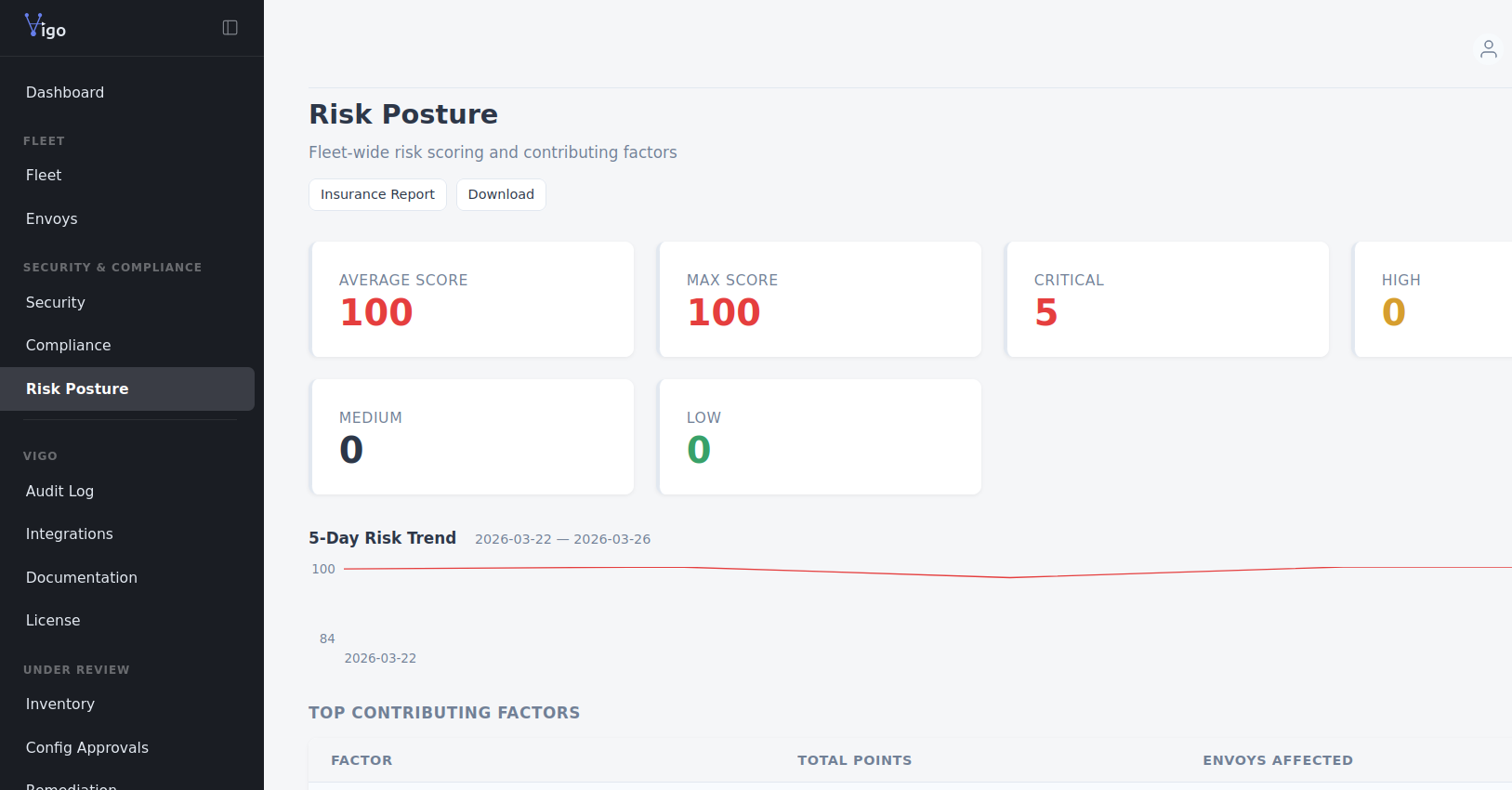
Security
Zero trust. No exceptions.
mTLS on all traffic. ED25519 request signing on every API call. One-time bcrypt tokens. Secrets never in plaintext — anywhere. No --no-ssl flag. No insecure mode.
Architecture

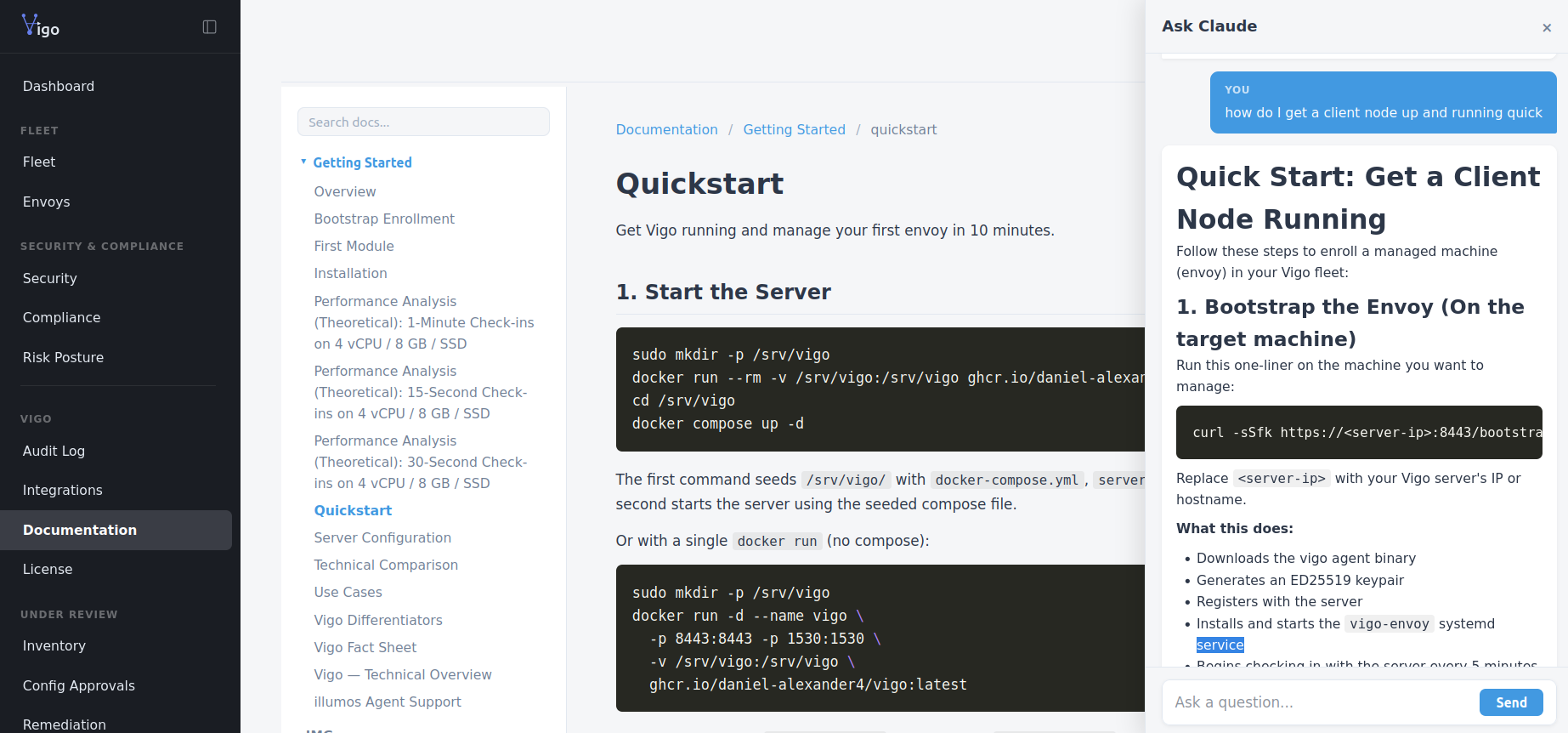
Server up and running with one command
docker run -d --name vigo -p 8443:8443 -p 1530:1530 -v /srv/vigo:/srv/vigo ghcr.io/daniel-alexander4/vigo:latest
That's it. TLS certificates, database, secrets, and example configs are auto-generated on first start. Open https://localhost:8443 to see the dashboard.
Agents enrolled in 30 seconds
curl -sSfk https://server:8443/bootstrap | sudo sh
Downloads the 5 MB agent binary. Generates TLS certificates. Enrolls with the server. Installs the system service. Verifies connectivity.
Works on Linux, macOS, FreeBSD, OpenBSD, NetBSD, and illumos.
Windows: irm https://server:8443/bootstrap?os=windows | iex
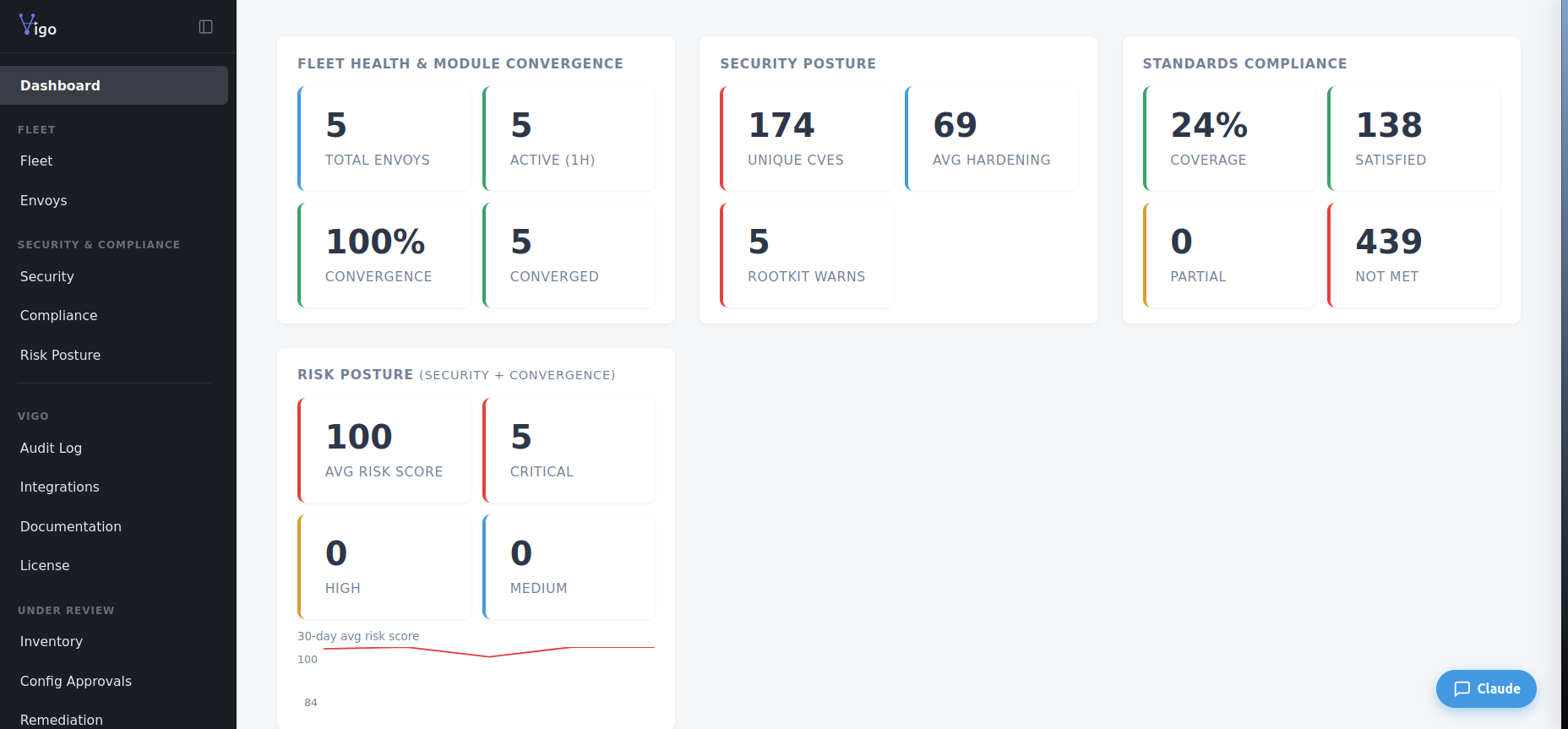
See everything at a glance
One config. Every platform.
Write type: service and the agent dispatches to the correct backend. No platform-specific configs required.
| Platform | Init System | Package Manager | Executors |
|---|---|---|---|
| Linux | systemd | apt, dnf, yum, zypper, pacman, apk | 58 types |
| macOS | launchd | Homebrew | 52 types |
| FreeBSD | rc.d | pkg | 53 types |
| OpenBSD | rcctl | pkg_add | 52 types |
| NetBSD | rc.d | pkgin | 51 types |
| illumos | SMF | IPS | 48 types |
| Windows | Windows Service | Chocolatey, winget, Scoop | 63 types |
| Network Devices | — | — | 16 SSH-based (Cisco, Arista, Juniper) |
Remote access from the browser
SSH terminals and RDP desktops in your browser. No VPN. No bastion host. No port forwarding. Through the same mTLS tunnel the agent already uses.
SSH
Full terminal via xterm.js. Ephemeral keys generated per session. No permanent SSH credentials stored on the server.
RDP
Graphical desktop via Guacamole. Fit-to-window or 1:1 scaling. Clipboard sync, file transfer, on-screen keyboard.
Shadow / Assist
See and control a user's live desktop session. Observe what they see in real time, or take the wheel to help. User consent prompts built in. Linux (x11vnc) and Windows (TightVNC).
Zero infrastructure
No jump boxes, no VPN concentrators, no SSH bastion. The agent tunnels through its existing gRPC connection. One fewer attack surface.
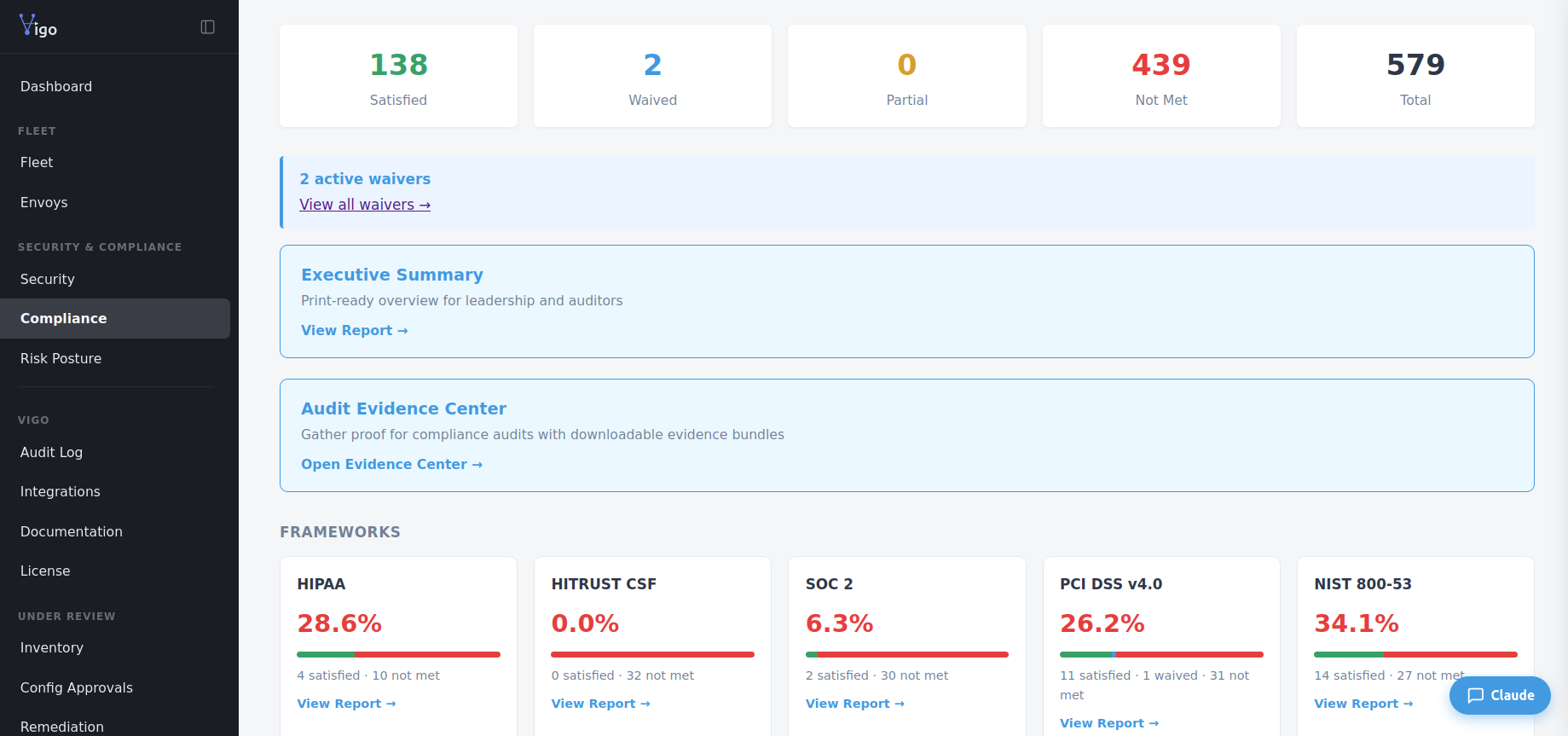
22 compliance frameworks. Enforced, not just reported.
Vigo maps module resources to regulatory controls and tells you exactly what it enforces, what it monitors, and what requires external validation. No overclaims.
HIPAA
Access controls, audit logging, encryption, session management
SOC 2
Change management, access provisioning, monitoring, availability
PCI DSS v4.0
Firewall, hardening, access control, integrity monitoring
NIST 800-53
AC, AU, CM, IA, SC control families
CIS Benchmarks
Ubuntu, RHEL, Windows Server — 260+ controls
ISO 27001
Asset management, cryptography, operations security
Also: SOX, FINRA, MiFID II, GDPR, NERC CIP, HITRUST, IEC 62443, CCSS, FDA 21 CFR Part 11, Gaming Commission (NV/Malta/UKGC), DISA STIG, CIS Windows, Cyber Essentials, ABA Cybersecurity, NY DFS 23 NYCRR 500. Full framework list →
Observe before you enforce
Run Vigo alongside your existing configuration management. See exactly what it would change — without changing anything.
Per-node or fleet-wide
Enable observe mode globally in server.yaml or per-node in config. Agents report drift without applying changes.
Safe migration path
Enroll nodes managed by Puppet, Ansible, Chef, or Salt. See what Vigo would do. Cut over when you're confident.
Module retraction
Remove a module from config and Vigo cleans up: packages uninstalled, files deleted, services stopped. Opt-in per module.
Distribute anything. Peer-to-peer.
Swarm distributes files across your fleet using mTLS peer-to-peer transfer. No server bottleneck — agents share chunks directly. Vigosync takes it further: personal file sync across every machine where you have an account.
Swarm P2P
Content-addressed blobs distributed via CLI or seeded from any envoy. Rarest-first chunk scheduling, adaptive bandwidth, multicast peer discovery. Real-time progress tracking with per-chunk source visualization.
Vigosync
Drop a file in ~/vigosync/ on any machine. It appears on every other machine where you have an account. No config. No commands. Just the folder. Built on swarm P2P — fast, secure, zero-effort.
Server goes down? Agents keep working.
Agents cache signed policy bundles in LMDB. When the server is unreachable, convergence continues using the last-known policy. Results queue locally and drain automatically when connectivity returns. No other state enforcement engine offers this level of offline resilience.
* Free tier is for evaluation purposes only and is provided AS IS with no support obligation. See Commercial Terms.
